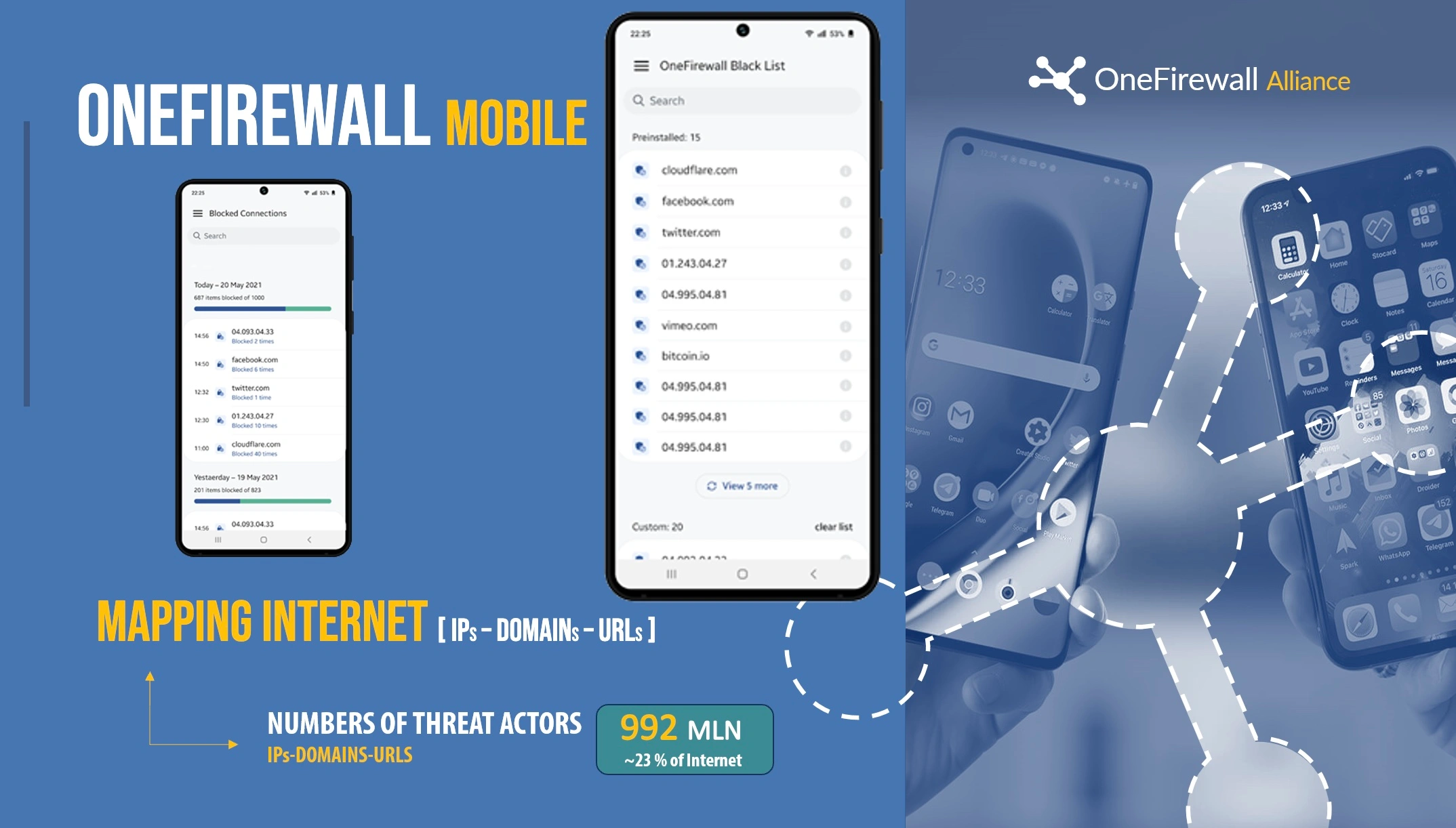
OFA Mobile
Mobile protection powered by the Alliance. Block malicious IPs, domains, botnets, and phishing in real time on Wi-Fi and cellular—inside and outside the corporate perimeter.
Mobile Security Without Blind Spots
OFA Mobile enforces Alliance-validated intelligence on the device. You are not relying on isolated detections—your mobile traffic is validated against what other members are already intercepting in production.
What it does
- Creates a local security tunnel and evaluates connections before they complete
- Blocks known malicious IPs/domains and repeat attacker infrastructure
- Prevents outbound connections to botnet and command-and-control endpoints
- Protects users on public Wi-Fi, home networks, LTE/5G and roaming
- Uses intelligence shared by 210+ alliance members in near real time
Core capabilities
Real-time IoC enforcement
Botnet & C2 disruption
DNS + IP layer filtering
Phishing domain blocking
Policy-based controls
Central visibility (enterprise)
What you see in real time: blocked connections, attempted C2 callbacks, malicious DNS resolutions, and repeat attacker infrastructure identified across the Alliance.
Same intelligence, different perimeter: your users.
Why OFA Mobile
Most mobile security products depend on their own telemetry. OFA Mobile is backed by shared detections from other security operations—as if your devices benefit from what other SOCs are already blocking.
Where it fits
Remote workforce
Protect employees outside the office perimeter from malicious infrastructure and phishing domains, regardless of the network they are using.
Executive protection
Reduce exposure for high-value targets and traveling staff—common victims of credential theft, surveillance, and targeted malware delivery.
BYOD security
Extend enforcement-ready intelligence to unmanaged or semi-managed devices without requiring endpoint agent sprawl.
Deploy OFA Mobile with Alliance Intelligence
Get the same attacker infrastructure other alliance members are intercepting—applied to your mobile fleet. Request enterprise deployment details and licensing.
Test it on your Enviroment →