Stop Defending Alone - IoCs Validated Beyond Your Perimeter
Aggregate, validate, and consume CTI identified by 290+ alliance members and CTA partners. Convert distributed detection into centralized, automated blocking across firewalls, IPS, WAF, SIEM, and cloud controls!
Premium & Actionable Threat Intelligence (CTI)
Intelligence Overview
- Aggregated and enriched intelligence feeds Crime Score
- Real-time updates
- Designed for direct firewall enforcement
- Reduces need for multiple security vendors
- Built for SOC teams and MSSPs
Intelligence Capabilities
IP Reputation Feeds
Botnet Tracking
Malicious ASN Detection
Threat Actor Monitoring
IOC & CTI Automation
Real-time Distribution
What We Do
Threat Intelligence Alliance
Crowd-sourced threat intelligence covering IPs, domains, URLs, and malware. Over 210 alliance members sharing vetted intelligence.
Automated Prevention
Real-time synchronization with IPS, XDR, firewalls, WAFs, and routers for automated threat blocking.
Mobile & Endpoint Protection
Self-routing local VPN application protecting devices from malicious inbound and outbound traffic.
Enterprise VPN & DNS
Workplace-dedicated VPN and secure DNS services powered by alliance threat intelligence.
AI Gateway Security
Specialized firewall for AI public services preventing data leakage while enabling safe AI usage.
Offensive Security
Comprehensive DAST, dark web scanning, and penetration testing to validate defensive posture.
Why OneFirewall
Proud Member of the Cyber Threat Alliance since 2020
Sharing vetted intelligence globally to strengthen collective cyber defence.
Learn More About Our Membership →

The Cyber Threat Alliance (CTA) is working to improve the cybersecurity of our global digital ecosystem by enabling near real-time, high-quality cyber threat information sharing among companies and organizations in the cybersecurity field. cyberthreatalliance.org →
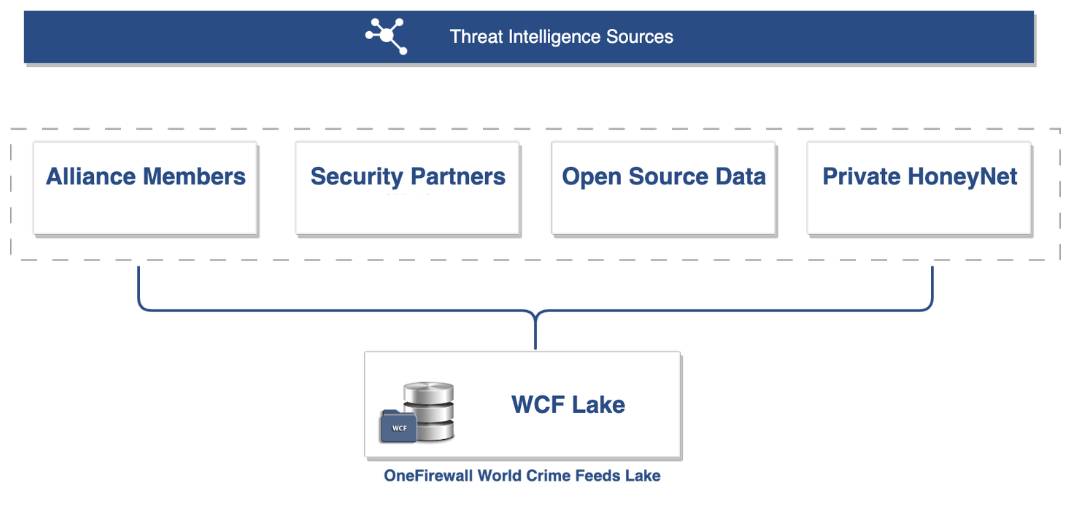
Architecture Overview
Intelligence Ingestion
Threat Validation
Enrichment Layer
Distribution Engine
IPS Synchronization
Real-Time Prevention
Honeynet
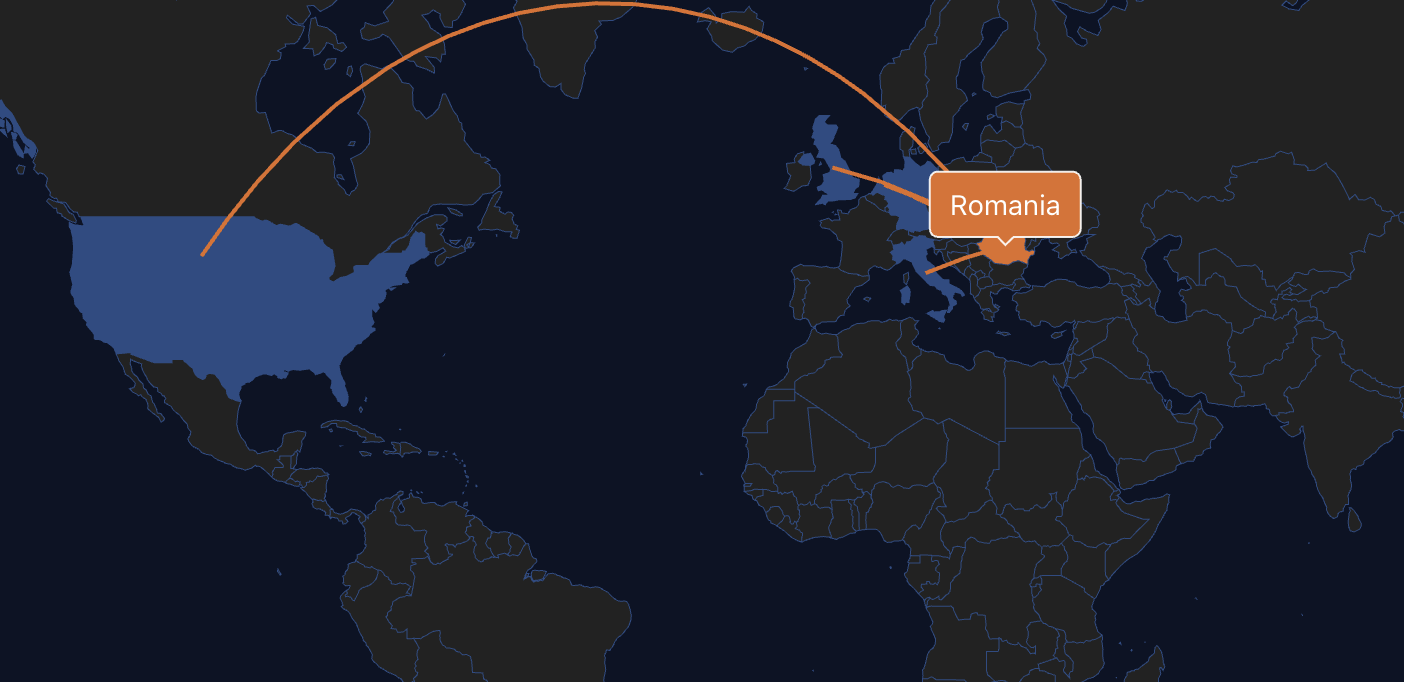
DeceptionGrid is OneFirewall’s global honeynet: geographically distributed, high-fidelity honeypots designed to attract attackers and turn their activity into actionable threat intelligence.
Each node simulates believable environments (services, banners, and behaviors) to lure scans and targeted probing, record sessions and traffic, and extract IOCs, TTPs, and attacker fingerprints that enrich the OneFirewall Threat Intelligence Data Lake.
🛰️ Distributed Honeypot Network
Strategically deployed nodes across regions to maximize visibility into real-world adversary activity and emerging threat patterns.
🎭 High-Fidelity Decoy Services
Nodes expose realistic services (remote access, web/API, IoT/OT, databases, cloud/DevOps) to attract different attacker profiles.
📼 Full Telemetry
Session recording, packet capture, and real-time logging to observe intent, tooling, and tradecraft—then correlate at scale.
⚡ Intelligence → Defense
Findings are converted into IOCs/TTPs and fed back into OneFirewall’s platform to strengthen prevention and reduce attack surface.
What’s simulated on each node
🔐 Network & Remote Access
- SSH (22), Telnet (23)
- RDP (3389)
- VPN Gateways (e.g., OpenVPN/IPsec)
🌐 Web & API
- HTTP/HTTPS (80/443)
- REST APIs (custom ports)
- WebSockets endpoints
🏭 IoT & OT Protocols
- Modbus (502), MQTT (1883)
- UPnP/SSDP
- BACnet (47808), Zigbee (simulated)
🧱 Data, File & Databases
- FTP/SFTP, SMB/CIFS (445), NFS (2049)
- ElasticSearch (9200)
- MySQL, PostgreSQL, MongoDB, Redis, Cassandra
☁️ DevOps & Cloud
- Docker API (2375)
- Kubernetes API/Kubelet (10250)
- Jenkins (8080), GitLab (8929)
📨 Auth, Email & Messaging
- SMTP (25), IMAP (143), POP3 (110)
- LDAP/LDAPS (389/636), Kerberos (88)
- OAuth/OIDC endpoints
How it works
Lure & Engage
- Nodes respond to scans and probing with realistic service banners and behaviors.
Record & Analyze
- Activity is logged, enriched, and correlated in real time.
Extract Intelligence
- Behavior is converted into IOCs, TTPs, and attacker fingerprints.
Feed Defense
- Threat data is shared into OneFirewall’s platform to strengthen prevention.